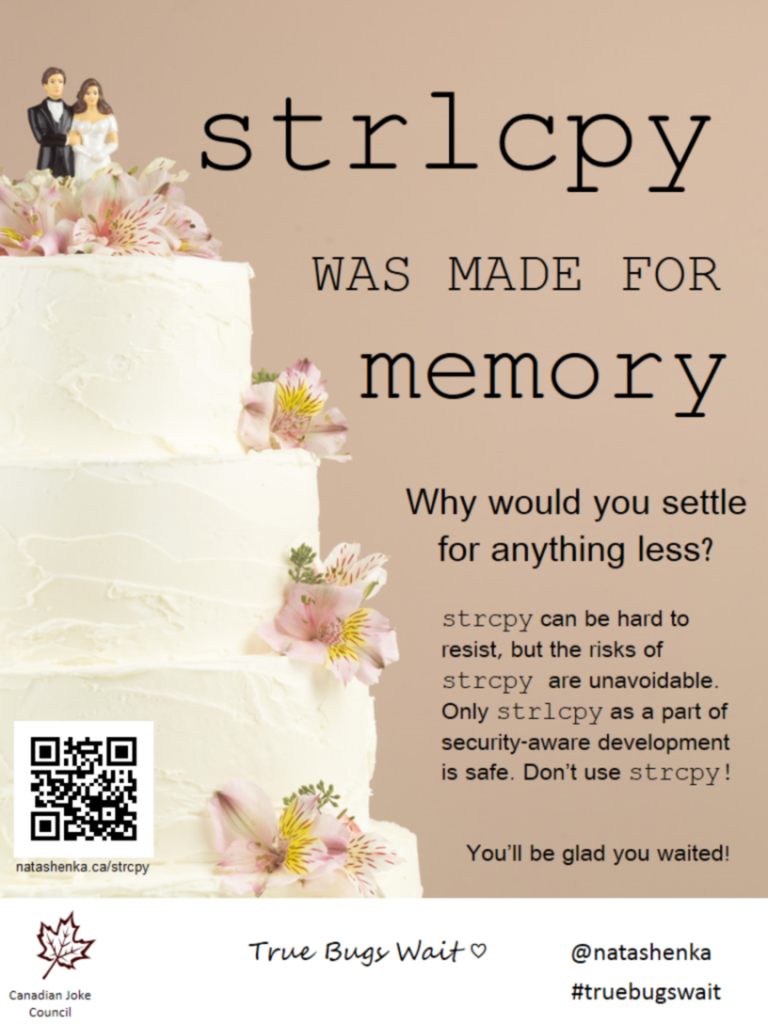
strcpy is unsafe because it doesn’t check the length of the destination buffer. This can cause the function to overflow the destination buffer when the input buffer is unexpectedly long, leading to security issues and application instability.
strlcpy and strcpy_s should be used instead of strcpy. Avoid using strncpy as a safe alternative to strcpy, as it does not null terminate the destination string in all circumstances.